What is Skydock? A Comprehensive Solution for CyberArk Object Migration
February 18, 2025
|
Duration:
8
min READ

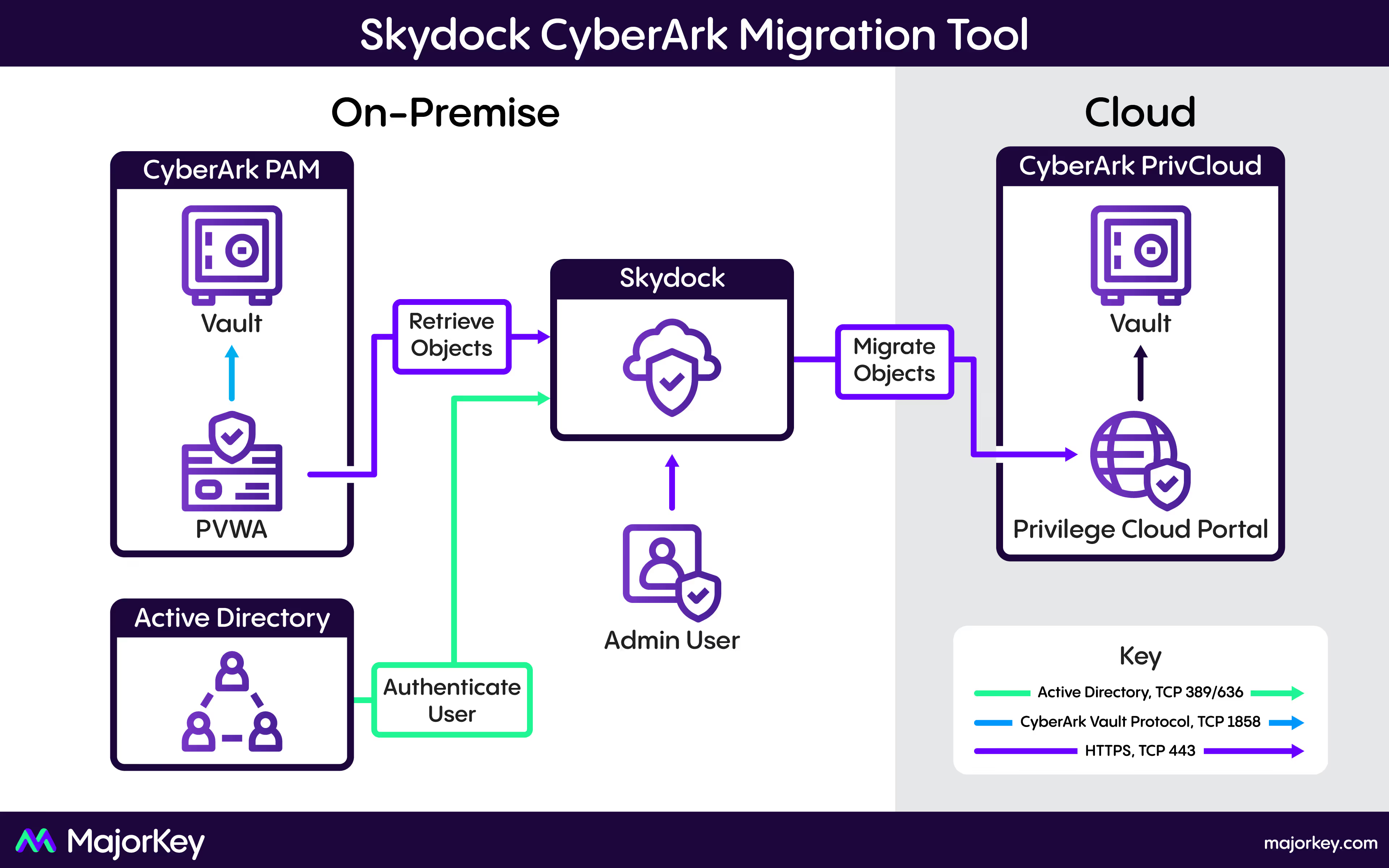
SkyDock is a robust ASP.Net Core solution designed to facilitate the seamless migration of CyberArk objects between different instances, including from on-premises installations to Privilege Cloud. With key features like Safe Member mapping, event log data collection using CyberArk's Export Vault Data Utility (EVD), threading to reduce migration time, selective object migration, and strict security protocols ensuring that secrets are never stored or persisted, SkyDock provides organizations with a reliable and secure tool for migration.
What is the purpose of Skydock?
The primary purpose of SkyDock is to automate and streamline the migration of CyberArk objects such as users, safes, platforms, and applications. This tool is particularly valuable for organizations looking to upgrade or reconfigure their CyberArk environments or transition from on-premises to Privilege Cloud. SkyDock minimizes downtime, reduces manual intervention, and ensures that all critical data and configurations are accurately transferred.
Core Features of Skydock
1) Seamless Migration Process
- Automated Object Transfer: SkyDock automates themigration of various CyberArk objects, including user groups, users, platforms,applications, safes, safe members, and accounts. This automation reduces therisk of errors and ensures a consistent migration process.
- Selective Object Migration: SkyDock provides theflexibility to select specific CyberArk objects for migration. This featureallows organizations to migrate only the necessary components, optimizing the migrationprocess and focusing on critical assets.
- REST API Utilization: SkyDock leverages the CyberArkREST API to facilitate secure data transfer between source and destinationenvironments, crucial for on-prem to cloud migrations.
- Secrets Management: A critical aspect of SkyDock isthat secrets contained in accounts are never stored or persisted in SkyDock’s database. These secrets are retrieved from the source environment only at thetime of migration and immediately transferred to the destination environment.This ensures that sensitive data remains secure and is not exposed or storedunnecessarily.
- Threading for Efficiency: SkyDock utilizes threadingduring the migration process to parallelize operations, significantly reducingthe overall migration time. This is especially beneficial in large-scale migrationswhere time efficiency is critical.
- Validation and Error Handling: SkyDock includesbuilt-in validation steps to ensure that all objects are correctly transferred.In case of errors, SkyDock’s robust error-handling mechanisms can retry operations,roll back partial migrations, or flag issues for manual resolution.
2) Safe Member Mapping
- Permission Consolidation and Redefinition: SkyDock’sSafe Member mapping feature allows organizations to consolidate or refinepermissions during migration. For example, individual user permissions in thesource environment can be mapped to roles or groups in the destination environment,streamlining access control management.
- Custom Mapping Rules: Administrators can definecustom mapping rules to tailor the migration process, ensuring that thedestination environment’s permission structure aligns with organizational policiesand security requirements.
3) Event Log Data Collection Using EVD
- Comprehensive Data Capture: SkyDock integrates withCyberArk’s Export Vault Data Utility (EVD) to capture detailed event logs fromthe source environment. This ensures that all user activities, system events,and security incidents are documented and retained.
- Retention Policy Compliance: The collected logs arestored in a centralized repository within SkyDock, allowing organizations tocomply with retention policies and maintain access to historical event data, evenafter migration to the cloud.
- Audit and Forensic Capabilities: The availability ofcomprehensive logs post-migration supports audit readiness and enhancessecurity by providing a clear trail of all system activities.
4) Handling On-Prem to Privilege Cloud Migration
- Mapping On-Prem Features to Cloud: SkyDock includeslogic to map on-prem features to their equivalents in Privilege Cloud. Thisensures that all critical security and operational features are preserved, orappropriately adjusted, during the migration.
- Seamless Data Transfer: SkyDock handles the securetransfer of data and configurations, ensuring that all elements of the CyberArkenvironment are accurately and efficiently migrated to Privilege Cloud.
- Post-Migration Benefits: After the migration,organizations benefit from a well-structured and consistent environment inPrivilege Cloud in-line with their previous instance.
Security and Compliance Capabilities
SkyDock is designed with security and compliance as a priority. By ensuring that secrets are never stored or persisted, by utilizing threading to enhance efficiency, by allowing selective migration of objects, and by maintaining detailed logs and audit trails, SkyDock helps organizations meet regulatory requirements and internal security standards.
In Conclusion
SkyDock is a comprehensive solution for organizations looking to migrate their CyberArk environments, whether upgrading on-prem installations or transitioning to Privilege Cloud. With features like Safe Member mapping, event log data collection via EVD, threading to reduce migration time, selective object migration, strict secrets management, and robust automation, SkyDock simplifies the migration process, reduces risks, and ensures that all critical security and operational needs are met.
Authors

No items found.
No items found.
No items found.
.svg)



















.svg)
