
Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Industries
Partners
© MajorKey 2025

Most IAM programs aren’t failing technically. They're failing because leaders can’t clearly demonstrate the business value IAM delivers.
Executives continue to invest in identity platforms, yet many IAM leaders still struggle to clearly answer a simple question from the business: What value are we actually getting from this?
Too often, the answer comes back in the form of dashboards, features enabled, or projects completed, rather than proof of reduced risk, simplified audits, or faster, safer access.
That disconnect is becoming harder to ignore.
In a recent LinkedIn Pulse article, industry analyst Jay McBain of Omdia highlighted a major shift underway in cybersecurity. Global cybersecurity spend is projected to reach $311 billion, growing 12.1% year over year. But the real story isn’t the size of the market. It’s where the money is going.
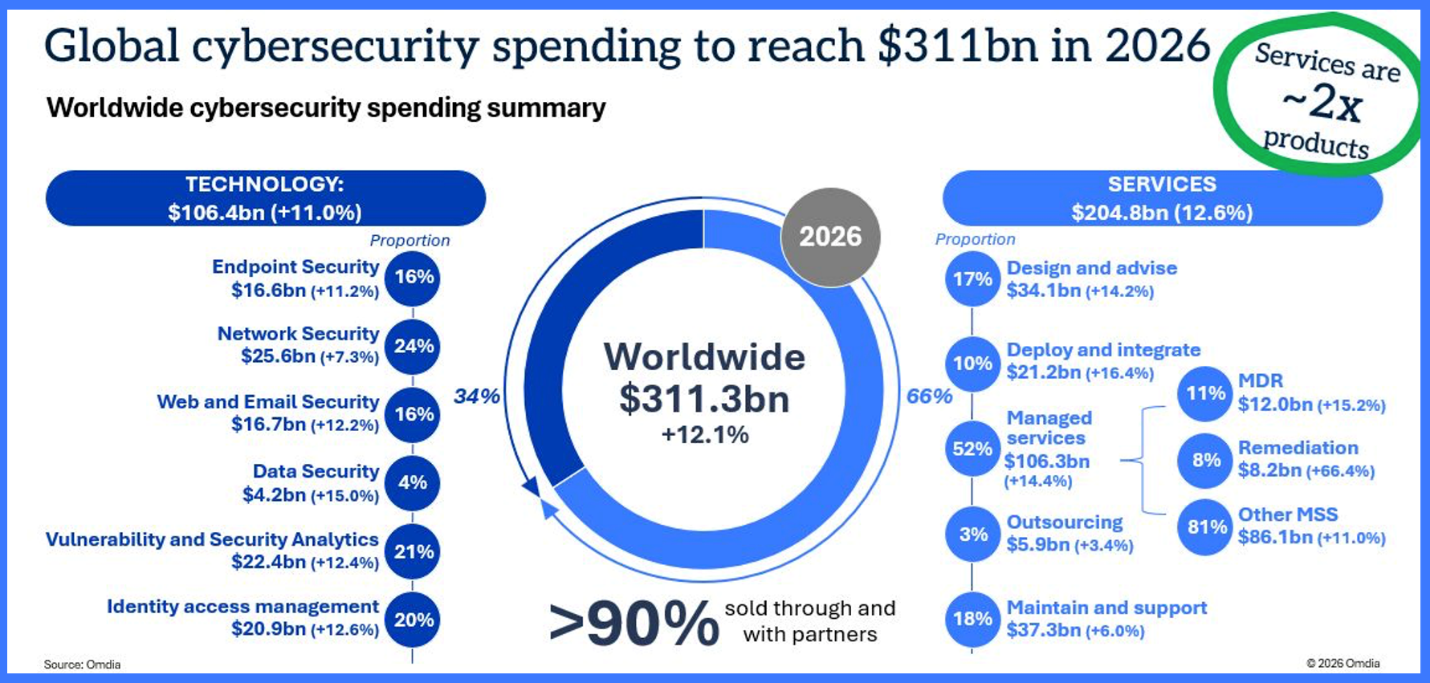
Buyers are moving away from simply purchasing tools and towards buying outcomes. Partner‑led and services‑driven models now account for the majority of cybersecurity delivery, as organizations prioritize continuous risk reduction, compliance confidence, and operational resilience over standalone technology. Identity is explicitly called out as one of the fastest-growing areas in this shift.
That macro trend mirrors exactly what we see every day inside identity and access management (IAM) programs:
IAM isn’t failing because organizations aren’t investing, or because the technology is flawed. The perception of failure stems from poorly defined success criteria, often set by the wrong stakeholders and communicated to the wrong audience. When success is measured without regard to who is impacted and what they need to see, event effective IAM program can appear unsuccessful.
Real progress only becomes visible when outcomes are defined in ways that are meaningful and relevant to every stakeholder involved.
Most enterprises today have invested heavily in IAM technologies, including identity governance (IGA), workforce IAM, privileged access management (PAM), authentication, and cloud identity platforms. On paper, the stack looks mature.
Yet IAM leaders are still asked uncomfortable questions:
In practice, many organizations see the same warning signs:
The gap between IAM capability and IAM performance is where many programs stall. As McBain’s analysis makes clear, buyers aren’t looking for more tools. They want risk reduced, compliance met, and breaches prevented continuously. That expectation is especially true in IAM, where identity now functions as the enablement plane for security, compliance, and digital business.
At MajorKey, we believe IAM success cannot be defined by feature checklists or go‑live milestones. It must be defined by measurable outcomes that both security leadership and the business understand.
This is especially important when success is measured using static metrics, while IAM itself supports highly dynamic activities—users change roles, access needs evolve, and risk conditions shift continuously. When outcomes aren’t aligned to that reality, even well‑implemented IAM programs can appear unsuccessful.
Our perspective is grounded in a simple principle:
Technology creates potential. Outcomes require operationalization.
Deploying an IAM platform may enable controls, but it doesn’t guarantee that those controls are effective, trusted, or sustained. Outcome-driven IAM focuses on what happens after implementation, when identity systems must perform reliably through organizational change, audits, and real-world incidents. It ensures alignment to business goals.
Outcome‑driven IAM is an approach that measures identity success by business and security results, not by the number of tools deployed or features enabled.
Instead of asking “Did we enable the feature?”, outcome‑driven IAM asks:
At MajorKey, outcome‑driven IAM rests on three foundational pillars.
You cannot govern identity without visibility.
Outcome‑driven IAM begins with unified visibility across identity systems, including IGA, PAM, directories, cloud platforms, and adjacent systems. Leaders must be able to answer, with confidence:
Visibility is not about collecting more data. It’s about actionable insight that supports decision-making, audit readiness, and timely remediation. Without trusted visibility, identity metrics become noise rather than evidence.
Manual IAM processes don’t scale, and they rarely survive organizational change.
Outcome‑driven IAM uses automation to:
When careful automation is applied intentionally, IAM shifts from a reactive security function to dependable enterprise infrastructure, where access is provisioned and removed in hours, not weeks, and controls don’t depend on heroics. Careful automation accounts for ensuring optimization without garbage-in-garbage-out.
This is where many IAM programs quietly fail.
Outcome‑driven IAM treats identity as an operating model, not a one‑time project:
Without an operational model, IAM slowly degrades. Roles drift. Exceptions accumulate. Controls that once passed audits lose integrity over time. Sustained outcomes require ownership, measurement, and continuous execution.
For executives, outcomes answer “Why does this matter?”
For IAM teams, outcomes answer “Is this actually working?”
For business owners, outcomes answer “What is in it for me?”
Meaningful IAM outcomes include:
In healthcare, this can mean clinicians receiving the right access at the right moment, without delays or unsafe workarounds. In regulated industries, it means proving compliance continuously rather than defensively.
MajorKey is built for organizations operating in complex, real‑world identity environments, not greenfield labs.
Our model focuses on moving IAM from vision to value through:
Across all of this, the focus remains the same – measurable outcomes over technical activity.
Jay McBain’s analysis underscores a broader cybersecurity reality. Organizations are shifting from buying tools to buying outcomes. IAM may be the clearest example of why this shift matters.
When IAM success is measured by outcomes, including reduced risk, governed access, simplified audits, minimized friction, and clear business enablement, identity programs earn executive trust, sustained funding, and long‑term relevance. Identity is now infrastructure. And infrastructure must work consistently, measurably, and continuously.
That’s why the future of IAM isn’t technology‑driven. It’s outcome‑driven.
If you had to prove today how your IAM program reduces business risk or enables the organization, could you do it without exporting data or creating a one-off report?
If not, it may be time to rethink how success is defined.
This article makes no reference to AI, and that is intentional. Identity security is more fundamental than AI. Without strong identity foundations, AI initiatives introduce risk faster than they deliver value. Effective identity security should enable, govern, and strengthen an organization’s AI ambitions, not attempt to catch up to them after the fact.
Outcome‑driven IAM is an approach that measures identity success by business and security results, such as reduced risk, audit readiness, and operational efficiency, rather than by tools deployed or features enabled.
Traditional IAM focuses on implementing technology. Outcome‑driven IAM focuses on operationalizing identity through visibility, automation, and ongoing governance so controls work continuously after go‑live.
IAM programs often fail because success is measured by deployment milestones instead of outcomes. Without visibility, automation, and operational ownership, identity controls degrade over time and fail to deliver measurable value.
IAM leaders should measure outcomes such as:
IAM has become the control plane for modern security, governing access across cloud, SaaS, and hybrid environments. As identity complexity grows, organizations must focus on continuous governance and outcomes rather than static controls.
MajorKey delivers outcome‑driven IAM through advisory services, automation‑focused deployment, and managed operations that sustain governance, visibility, and measurable progress over time.
