
Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Industries
Partners
© MajorKey 2025
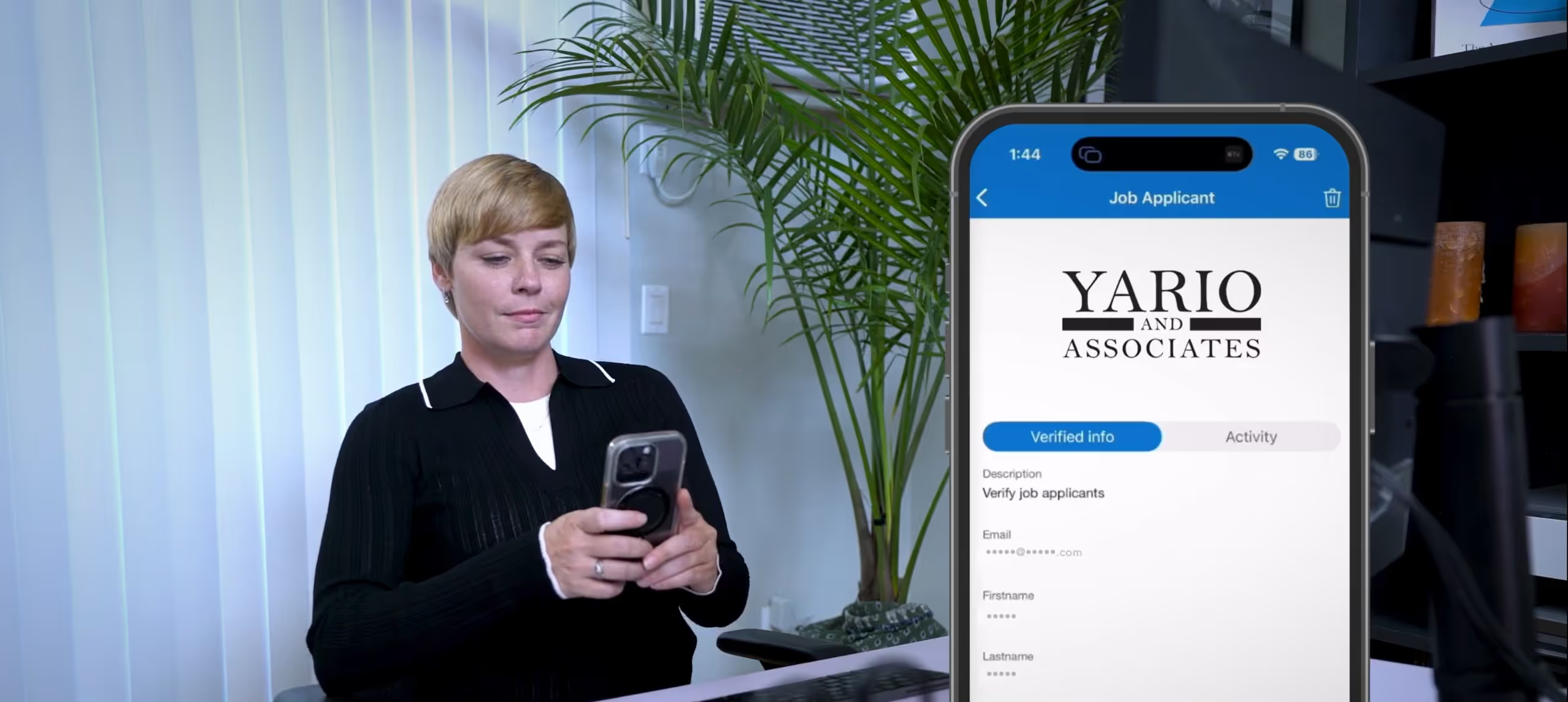
In our first blog, we introduced IDProof+, a rapidly deployable solution developed in collaboration with authID and integrated with Microsoft Entra Verified ID. It addresses critical vulnerabilities in remote identity verification, enabling organizations to confidently verify and maintain trust in remote individuals.
In this second installment, we explore why this issue is so pressing and why organizations can’t afford to ignore it.
Our global workforce has never been more diverse. Today, contractors, vendors, and external workers make up over 38% of the workforce. Combine that with the rise of remote work and inconsistent onboarding/offboarding processes, and the risks multiply.
Consider these sobering stats:
Remote work and contractor reliance have created a perfect storm–and hackers know it.
The threat isn’t hypothetical–it’s real. Here are a handful of recent real-world examples:
And the tactics keep evolving:
These threats underscore a critical truth: definitive identity assurance is no longer optional—it’s essential. IDProof+ delivers that assurance by binding an identity to a government-issued ID and biometric verification, ensuring organizations can trust who they’re hiring, onboarding, or supporting.

See IDProof+ in action and discover how it stops deepfake fraud and insider threats before they happen.
In our next and final blog, we’ll dive into three high-risk use cases—remote hiring, contractor onboarding, and help desk callers—and show how IDProof+ verifies users quickly and securely in each scenario.
Ready for a tailored walkthrough for your organization? Book your personalized demo today.
Remote work and contractor reliance have created new vulnerabilities. Nearly 50% of organizations have experienced breaches involving third-party access, costing an average of $4.88 million per breach. Fraudulent employees and deepfake tactics make identity verification essential.
IDProof+ is a rapidly deployable identity assurance solution developed in collaboration with authID and integrated with Microsoft Entra Verified ID. It binds an identity to a government-issued ID and biometric verification, ensuring organizations can trust who they hire, onboard, or support remotely.
It is very real. Examples include:
By combining government ID validation and biometric verification, IDProof+ ensures the person you’re hiring or onboarding is who they claim to be—closing gaps exploited by deepfakes and fraudulent employees.
Any organization with:
You can book a personalized demo to see how IDProof+ stops deepfake fraud and insider threats before they happen.
1 https://www.ibm.com/reports/data-breach
2 https://cloud.google.com/security/resources/m-trends
3 https://deepstrike.io/blog/deepfake-statistics-2025
6 https://www.sangfor.com/blog/cybersecurity/marks-spencer-cyberattack-2025-supply-chain-breach