
Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Industries
Partners
© MajorKey 2025
In today’s complex IT environments, visibility isn’t a luxury–it’s a necessity. That’s why we’re excited to announce the integration of IdentityLens into our Managed Operations (MOps) offering. This enhancement is already reshaping how we deliver value, giving our clients deeper insight, faster action, and stronger governance.
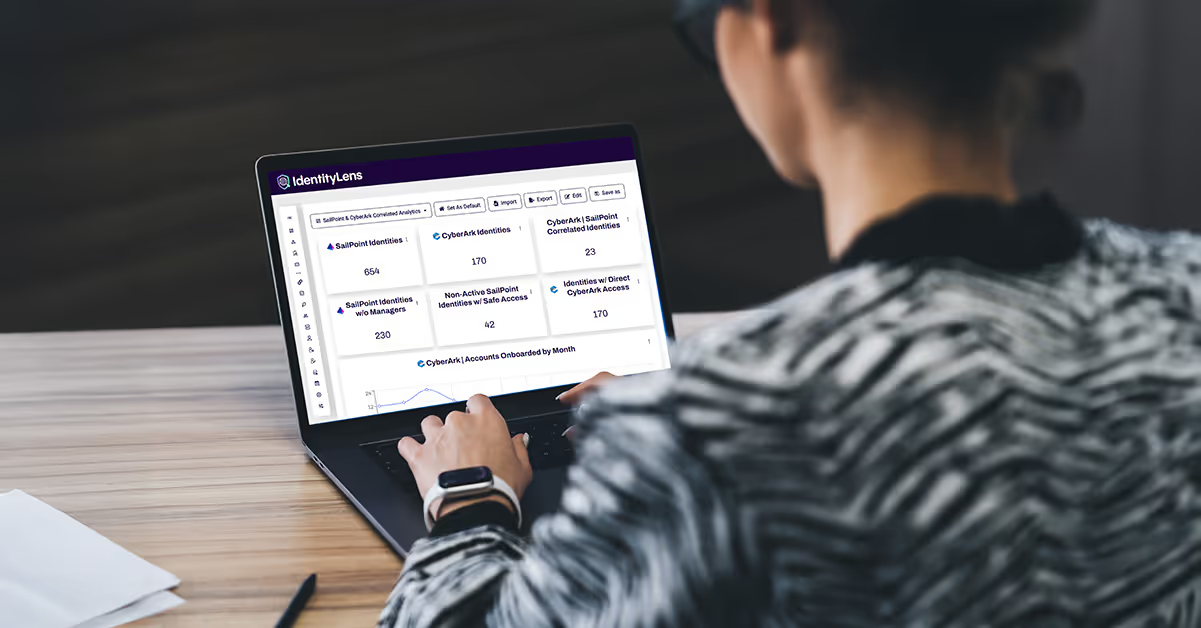
IdentityLens is a purpose-built reporting and analytics platform designed for cybersecurity and identity programs. It consolidates identity data from across your ecosystem into a single, actionable view–making it easier for clients to understand who has access to what, across which systems, and why.
For MOps clients, this means:
By embedding IdentityLens into our MOPs engagements, we’re giving clients a foundational product that:
And we’re not stopping there. As a MOps client, you’re eligible for a baseline IdentityLens deployment at no additional cost. From there, you can expand into advanced capabilities–like integrating additional data sources, customizing dashboards, or triggering automated provisioning directly from reports.
The demo video is live, showing how IdentityLens integrates with MOps to deliver real-time insights and operational clarity. If you’re already a MOps client, complete the opt-in form so you can request your baseline deployment. Not a MOps client yet? Let’s talk.
