
Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Industries
Partners
© MajorKey 2025
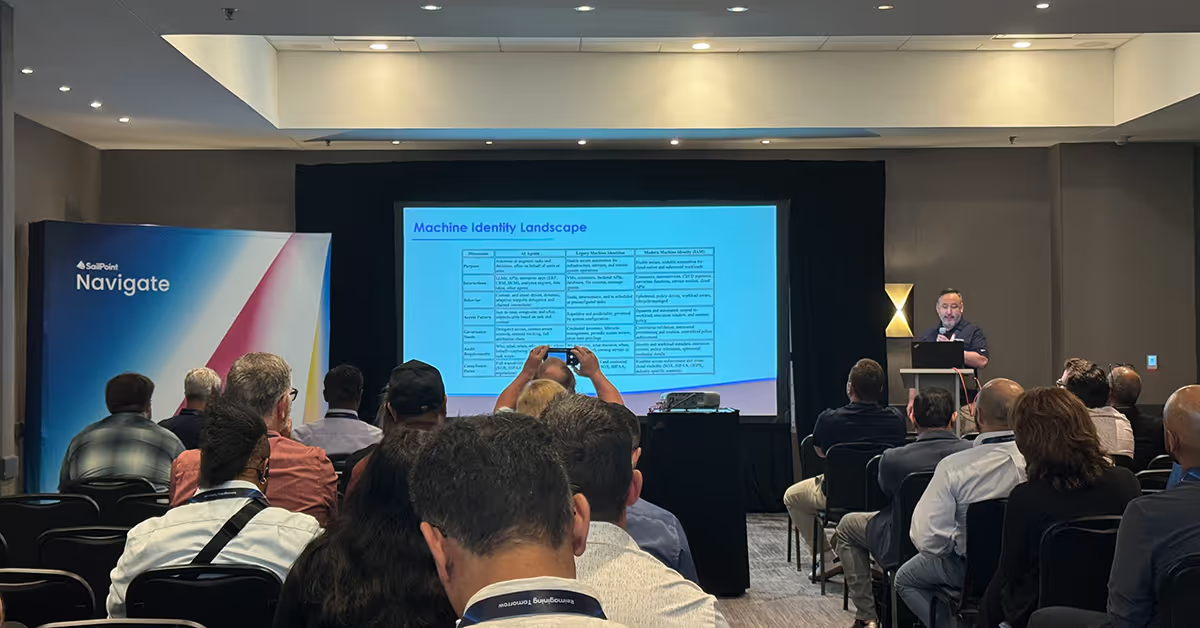
One of the biggest themes at this year’s SailPoint Navigate was the explosive growth of machine identities. With machines now outnumbering humans by staggering ratios, unmanaged identities have become a critical, and often overlooked, attack vector that organizations can no longer afford to ignore.
We explored this topic during our session, “From Shadow to Certainty: Securing Machine Identities with Confidence,” presented by MajorKey’s Director of IAM Services, Phil Martinez. If you weren’t able to attend live, keep reading to discover why machine identities are critical, the risks they pose, and how to secure them with confidence.
Machine identities, such as service accounts, API tokens, containers, and more, are the fastest growing identity management segment. Gartner estimates machines outnumber humans by a staggering 45:1, and nearly half of organizations experienced breaches linked to compromised machine identities last year. In 2024 alone, over 39 million secrets were leaked on GitHub, with high-profile incidents at companies like Microsoft and T-Mobile underscoring the urgency for proactive machine identity security.
Legacy identities are static and manual, relying on stored secrets and broad access. Modern identities are dynamic, ephemeral, and policy-driven, leveraging just-in-time (JIT) credentials and automated lifecycles. Moving from legacy to modern reduces risk and aligns with zero trust principles.
In traditional workforce identity management, responsibilities are fairly linear: Human resources manages people and lifecycle events, Security oversees policies and controls, and IAM teams handle access and governance. This structure works well for human identities, but machine identities shatter this mold.
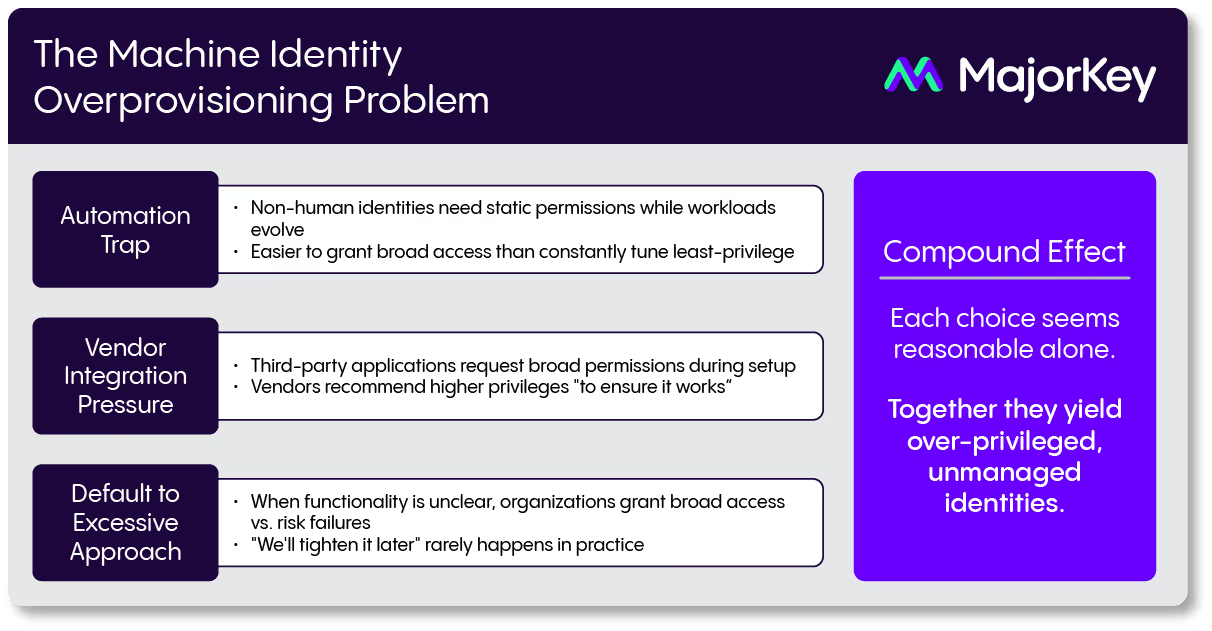
With machine identities, accountability becomes fragmented. DevOps, IAM, Security, and Platform teams all play a role, yet ownership is often unclear. A common pattern we see:
The result? Unmanaged, over-privileged identities lingering across your environment. Overprovisioning compounds this problem, as teams grant broad access for convenience and rarely revisit permissions. This accountability gap poses a serious risk, and demands a more collaborative, cross-functional approach to identity governance.
Traditional identity tools often fall short when it comes to uncovering the attack paths created by machine identities. For example, a user owning a service principal can add secrets, bypass MFA, and escalate privileges to Global Admin. These ownership relationships are frequently missed during certification campaigns, leaving dangerous blind spots for attackers to exploit.
Tools like Bloodhound can help uncover these hidden paths—surfacing risks that traditional reviews often overlook and giving security teams the visibility they need to take action.
Discovery alone isn’t enough; it’s just the beginning. To truly secure machine identities, organizations need automated classification, AI-powered detection, and seamless integration with governance workflows. Solutions like SailPoint’s Machine Identity Security go beyond visibility, helping group machine accounts by business applications, assign clear ownership, and feed into certification workflows.
Core features include:
Machine identities are multiplying, and so are the risks. The path forward requires more than technical fixes; it demands a strategic transformation. That means eliminating static credentials, embracing ephemeral identities, and embedding Zero Trust principles into every layer of your infrastructure. Continuous governance and AI-driven risk detection aren’t just best practices - they’re quickly becoming the standard.
This isn’t just a technical challenge. It’s an organizational imperative. Now is the time to align cross-functional teams, modernize identity workflows, and embed security into your development lifecycle from the start.
