
Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Industries
Partners
© MajorKey 2025

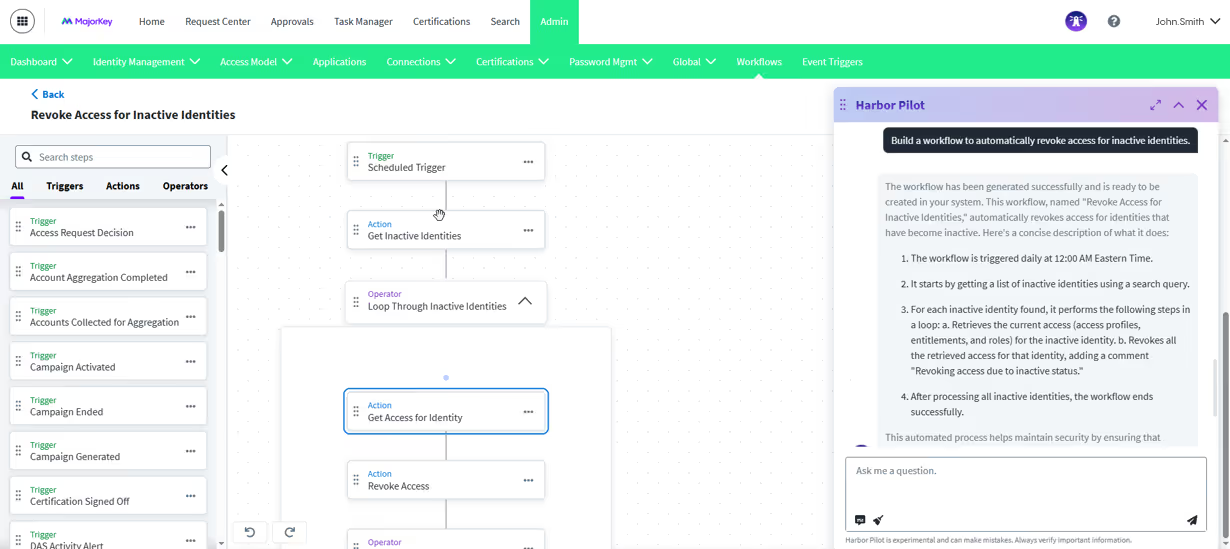
As identity security becomes more dynamic and complex, SailPoint’s latest innovation, Harbor Pilot, offers a compelling glimpse into the future of intelligent identity management. This agentic AI tool is designed to help teams work more efficiently by generating search queries, building workflows, and accelerating access to insights across SailPoint’s Identity Security Cloud (ISC).
We recently explored Harbor Pilot and gathered some early impressions from one of our IAM experts. Here is what stood out.
Harbor Pilot’s effectiveness depends on the quality of the prompts it receives. Like many AI tools, it performs best when given clear, well-structured input. Learning how to articulate requirements effectively is not only a quick win when using Harbor Pilot, but it is also a valuable long-term skill for engineers and consultants alike.
One of Harbor Pilot’s most helpful features is its ability to generate search queries using pre-built prompts. This is especially useful for admins who may not be familiar with all the searchable fields or syntax within ISC. It lowers the barrier to entry and helps users get to the right information faster.
Another promising area is workflow creation. While the workflows it generates are currently basic, they serve as a great starting point, particularly for those new to SailPoint. It is an excellent way to get comfortable with workflow design and can accelerate onboarding for junior team members.
As with any emerging technology, there are areas where Harbor Pilot is still evolving. For example, response times can vary, and the tool may not always reflect the very latest updates from SailPoint’s rapidly advancing platform. These are common challenges for AI systems in fast-moving environments, and we expect continued improvements as the product matures.
One enhancement that could further elevate the experience is the ability to retain context from previous interactions. While Harbor Pilot does not currently have memory across sessions, this is a natural next step that could make it even more intuitive and helpful over time.
Harbor Pilot is not intended to replace core responsibilities or expert judgment. Instead, it serves as a powerful complement, especially for newer users who need help getting unstuck or navigating specific tasks like search and workflow creation. It is also comparable to agentic AI offerings from other major players such as Okta and Microsoft, making it a strong addition to the broader identity ecosystem.
Harbor Pilot is a forward-looking tool that reflects SailPoint’s commitment to innovation in identity security. By helping users work smarter and faster, it has the potential to become a valuable collaborative tool for identity teams. As it continues to evolve, we are excited to see how it can support our work and enhance the way we engage with ISC.
The key takeaway is to stay curious. Explore what Harbor Pilot can do today and keep an eye on what it will do tomorrow.
