
Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Industries
Partners
© MajorKey 2025



Leading the way in identity strategic guidance
.svg)
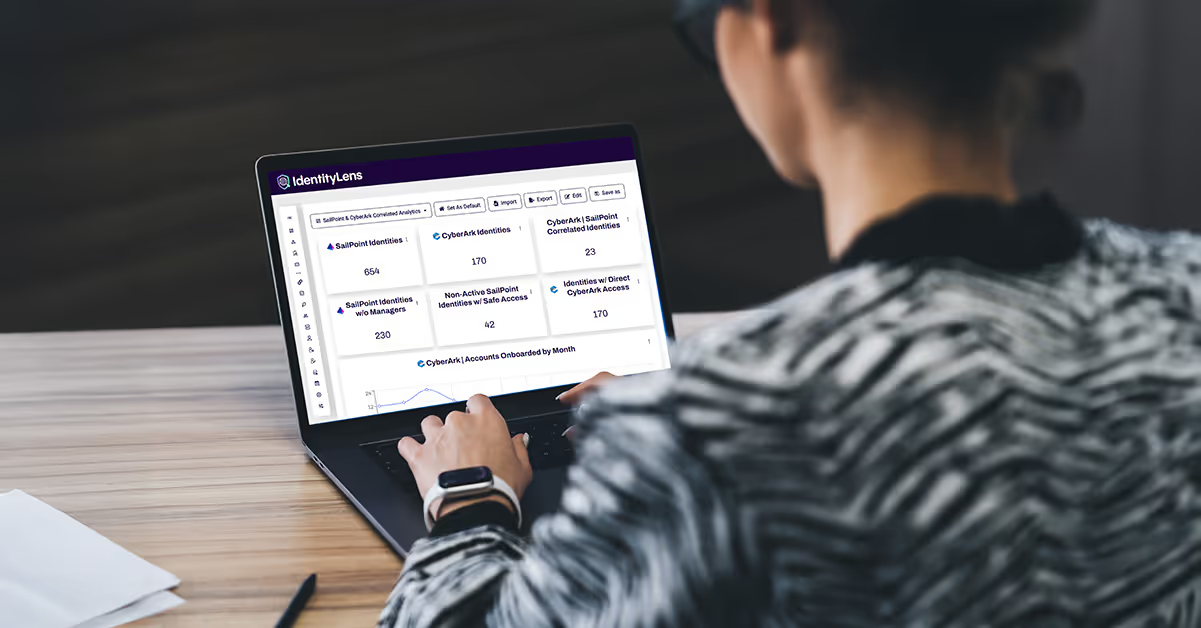
Our Advisory Services improves business outcomes through evaluation of risk, industry compliance, and business goals so you can meet challenges head on without getting stuck.
We guide customers on:



Our Advisors work across the technology and vendor landscape, extending expertise to your applications, cloud, and data systems.
.svg)
.svg)











































































































%20and%20Its%20Importance.avif)


















%20in%20IAM.avif)

%20in%20CIEM.avif)











.avif)


.avif)

.avif)

%20Definition%2C%20Importance%2C%20and%20Real-World%20Applications.avif)







.avif)















.avif)
















%20The%20Definitive%20Guide%20%5B2023%5D.avif)











%20%20An%20In-Depth%20Overview.avif)




















































































Covering the latest thought leadership, events, and news about identity security
.svg)